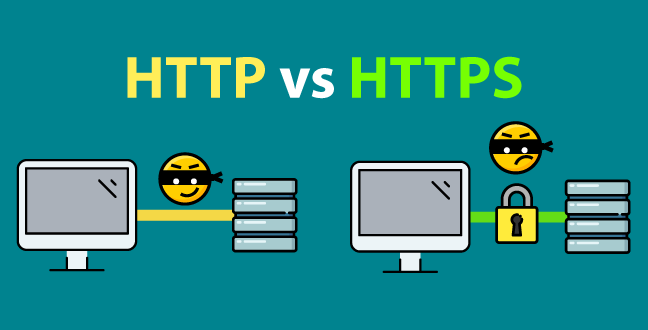
In the infrastructure of the digital world, HTTP and HTTPS are two terms that cannot be ignored. They represent not only two distinct technical protocols but also the civilizational evolution of the internet from its “wild west” era to the “age of security.”
I. HTTP: The Cornerstone Protocol of the Internet
HTTP (Hypertext Transfer Protocol) was born in an era when the concepts of data collection and analysis were still unknown. Its core logic is simple: I request, you respond.
Technical Features: It functions like an amazing conveyor belt, transporting information exactly as it is.
Limitations: Due to the lack of encryption, this “transparency” makes modern networks rife with danger. In an HTTP environment, every click and every string of characters is transmitted “in the open,” making them highly vulnerable to interception or hijacking.
II. HTTPS: The Trust Infrastructure of Cybersecurity
To reinforce this conveyor belt with steel plates, HTTPS (Hypertext Transfer Protocol Secure) made its debut. It introduces an SSL/TLS encryption layer on top of HTTP.
Core Logic: Through complex handshake protocols and key exchange, it ensures that data appears as gibberish during transmission, decryptable only by the target server.
Authentication: Digital certificates solve the real-world problem of “Is the website you’re visiting actually the one you think it is?”
III. The Multi-Dimensional Battle Between HTTP and HTTPS
| Dimension | HTTP(Traditional Mode) | HTTPS(Secure Mode) |
| Data Format | Plain text, as easy to read as a postcard | Encrypted text, as secure as a safe |
| Connection Cost | Low, extremely fast response | Slightly higher (requires encryption and decryption processing) |
| Search Ranking | Gradually devalued by search engines | Grants higher SEO ranking priority |
IV. Why Does Pure Encrypted Transmission No Longer Meet Modern Security Requirements?
Many users believe that as long as a website is upgraded to HTTPS, web access is completely secure. However, in practical business logic and complex operations, security is merely the baseline—not the end goal.
Yet, the simple HTTPS protocol faces new bottlenecks:
Geographic Blocking: Even if your connection is encrypted, if your IP location is identifiable, you may still be unable to access the target resource.
Identity Standardization: When conducting market research or operating mathematical platforms, a fixed IP address can cause your HTTPS connection to be flagged as “suspicious activity.”
Traffic Profile Exposure: Although the content is encrypted, your IP traffic patterns remain visible, which in a highly competitive business environment can lead to the leakage of trade secrets.
This means we need not only an encrypted channel (HTTPS) but also a flexible identity (native IP).
V. From Protocol Security to Unrestricted Access: Novproxy’s Advanced Solution
When the basic HTTPS protocol cannot support complex global operations, implementing high-quality proxy middleware becomes a common solution. It is against this backdrop that Novproxy provides developers and enterprises worldwide with a higher-dimensional network solution.
1. How does it complement HTTPS?
Novproxy does not alter the encrypted nature of HTTPS; instead, it builds upon it with an “invisibility cloak”:
Novproxy provides residential IPs spread across the globe, allowing you to freely switch IPs based on business needs when initiating HTTPS requests.
2. Key Technical Highlights of Novproxy
Authenticity of Residential IPs: Unlike cheap data center IPs, Novproxy’s residential IPs offer exceptional value and are the ideal choice for long-term account operations.
Full Protocol Compatibility: Whether it’s traditional HTTP or high-security HTTPS, Novproxy enables seamless forwarding, ensuring both data security and transmission efficiency.
Flexible Selection of Dynamic and Static Tasks: Supports automatic IP rotation based on needs or locking a single IP for extended periods, meeting all-scenario requirements from data collection to account load balancing.
VI. Summary: Building Your Comprehensive Network Solution
In today’s internet environment, relying solely on protocols is no longer sufficient to address rapidly evolving business challenges. Only by combining the security of HTTPS with the flexibility of Novproxy can you truly build a global network access system that is both secure and flexible.


